According to Microsoft's official disclosure, a serious security vulnerability has been exposed in the Windows system recently, numbered CVE-2024-38063.
The vulnerability affects all supported versions of Windows, including Windows 11, Windows 10, and multiple versions of Windows Server.

The CVSS3.1 score is 9.8 out of 10, which is critical and allows an attacker to remotely hack a device and execute arbitrary code through specially crafted IPv6 packets.
It is reported that the vulnerability was discovered by the Kunlun Lab, a subsidiary of the domestic security startup Cyber Kunlun, and was caused by an integer underflow bug.
This vulnerability exists in the TCP/IP network stack of Windows and is a serious remote code execution vulnerability.It affects all Windows systems with IPv6 enabled by default.

An attacker can repeatedly send specially crafted IPv6 packets to a Windows device to trigger the vulnerability and remotely execute code.No user interaction or authentication is required.
Microsoft strongly recommends that all users update to the latest Windows version as soon as possible.
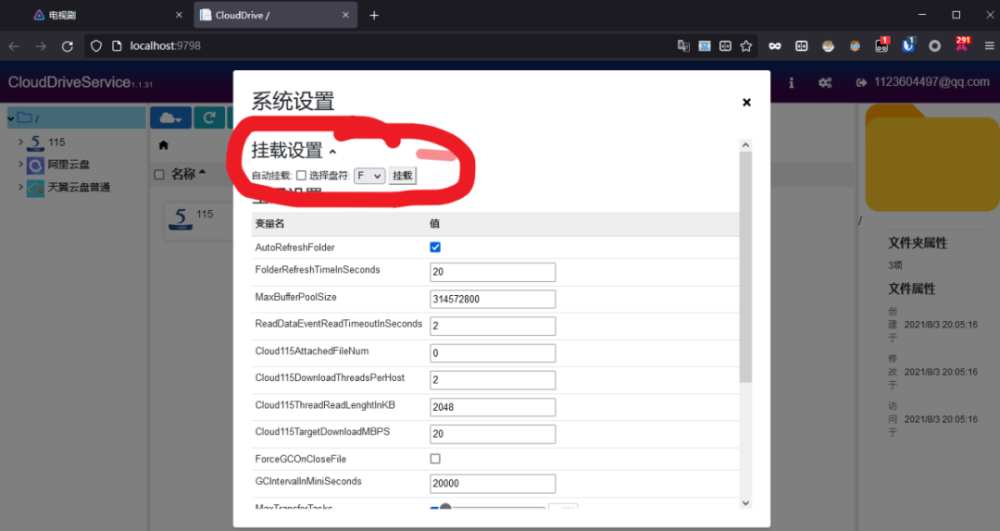
Microsoft is releasing a patch to fix this vulnerability, and disabling IPv6 temporarily prevents exploitation.
In most cases, the IPv6 address obtained by the user is a public IP address, so it is highly likely that an attacker will carry out targeted intrusion into a specific company, school, institution, or target group.
Thank you for visiting, please bookmark this site for more exciting articles.



















There are no comments yet